Elk For Cybersecurity
ELK for Security Analyst
- 4.721 students
- Last updated 25/7/2023
Course Description
This self-paced course takes you deep into the ELK Stack (Elasticsearch, Logstash, and Kibana) to enhance your security skills and become a sought-after Security Analyst. Starting from the basics of setup and configuration, you’ll progress through advanced log management techniques, search queries, and threat detection practices.
The course emphasizes hands-on lab work, giving you practical experience in setting up and optimizing ELK for security monitoring. You’ll learn key concepts in data ingestion, parsing, and visualization to create security dashboards that alert you to suspicious activity. Ideal for those looking to elevate their SOC and incident response capabilities using ELK.
What You Will Learn
- Set up and configure the ELK Stack from scratch.
- Analyze security events and logs effectively using Kibana.
- Detect threats by creating custom Elasticsearch queries.
- Parse log data with Logstash for security insights.
- Build interactive dashboards to monitor security metrics.
- Apply threat detection techniques using the ELK environment.
- Monitor security incidents with tailored alerting mechanisms.
- Manage and scale ELK deployments for large data volumes.
Who is this course for?
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Ut elit tellus, luctus nec ullamcorper mattis, pulvinar dapibus leo.
Course Content
 Introduction to Elastic Stack
Introduction to Elastic Stack
 Elastic Stack Components
Elastic Stack Components
 ELK Walkthrough
ELK Walkthrough
 ElasticSearch
ElasticSearch
 Kibana
Kibana
 LogStash
LogStash
 Beats
Beats
 Elastic Agents
Elastic Agents
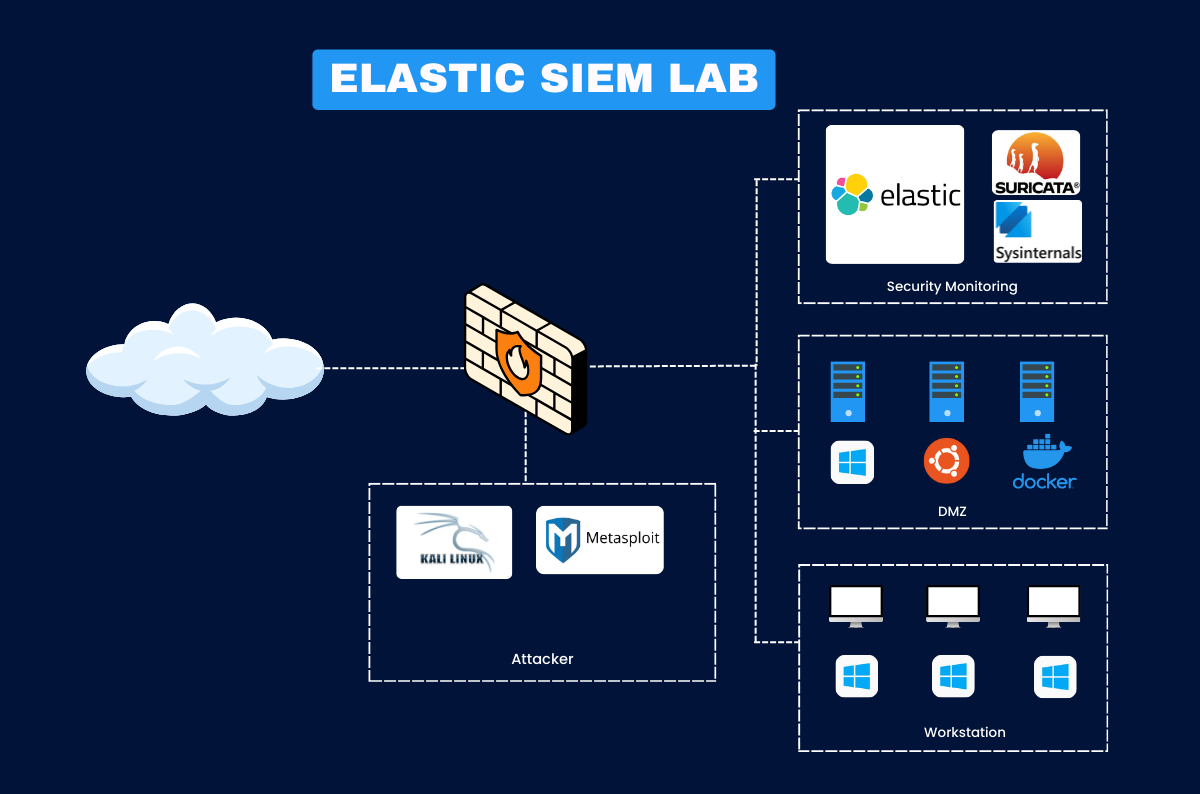
 Elastic Stack as SIEM
Elastic Stack as SIEM
 What is Fleet?
What is Fleet?
 Lab Set up: Installing ELK
Lab Set up: Installing ELK
 Lab Set up: Fleet Server Setup
Lab Set up: Fleet Server Setup
 Lab Set up: Installing Fleet on Ubuntu
Lab Set up: Installing Fleet on Ubuntu
 Task#1 Investigating Unauthorized SSH Access Attempts Using ELK SIEM
Task#1 Investigating Unauthorized SSH Access Attempts Using ELK SIEM
 Verify the ELK and Fleet Agent
Verify the ELK and Fleet Agent
 Simulate the attack and Visualize the events
Simulate the attack and Visualize the events
 Create Elastic Security rules, detect and Investigate
Create Elastic Security rules, detect and Investigate
 Task#2: Detecting Suspicious activities using SysmonForLinux
Task#2: Detecting Suspicious activities using SysmonForLinux
 Install SysmonForLinux
Install SysmonForLinux
 Prepare ELK for detection
Prepare ELK for detection
 Simulate the attack and visualize the events
Simulate the attack and visualize the events
 Task#3: Investigating File Integrity using Auditd
Task#3: Investigating File Integrity using Auditd
 Install Auditd
Install Auditd
 Prepare ELK for detection
Prepare ELK for detection
 Simulate the attack and visualize the events
Simulate the attack and visualize the events
 Lab Set up: Fleet Agent Windows Installation
Lab Set up: Fleet Agent Windows Installation
 Task 1: Investigating RDP Brute-Force Attacks on Windows Login
Task 1: Investigating RDP Brute-Force Attacks on Windows Login
 Installing Sysmon
Installing Sysmon
 Setting up ELK
Setting up ELK
 Simulate the attack and Visualize on ELK Dashboard
Simulate the attack and Visualize on ELK Dashboard
 Task 2: Investigating PowerShell Abuse on Windows Machines
Task 2: Investigating PowerShell Abuse on Windows Machines
 Simulate the attack and Visualize on ELK Dashboard
Simulate the attack and Visualize on ELK Dashboard
 Task 3: Monitoring Windows Registry Changes
Task 3: Monitoring Windows Registry Changes
 Setting up ELK
Setting up ELK
 Simulate the attack and Visualize on ELK Dashboard
Simulate the attack and Visualize on ELK Dashboard
Pre-requisites
- Basic networking and security concepts
- Fundamental knowledge of logs and log types
- Familiarity with Linux and command line
Instructor

Senior Security Consultant
- With over a decade of experience in cybersecurity and author of multiple works on security monitoring, Rajneesh is a trusted expert in open-source security tools, cloud security, and SOC automation. He has implemented and optimized ELK deployments for global clients and specializes in turning raw log data into actionable security intelligence. Rajneesh’s instruction style is both practical and thorough, ensuring you gain job-ready ELK skills.
This course includes:
- 8.5+ Hours of Learning Modules
- 10+ Attacks and Detections
- Certificate of Completion
- Lifetime Community Access
- Access on mobile and TV

Testimonial
What alumni say about us






FAQs
The ELK Stack consists of Elasticsearch, Logstash, and Kibana, used for log management and security monitoring.
No prior ELK experience is necessary, but familiarity with logs is helpful.
It’s self-paced, but most learners complete it in 4-6 weeks.
A Linux system, preferably Ubuntu, with basic command-line skills.
Yes, you’ll receive a completion certificate from HaxSecurity.
Yes, the course includes practical labs based on real security incidents.
Yes, the course is accessible on both desktop and mobile devices.
We provide email and forum support, and Rajneesh hosts live Q&A sessions.
Featured Online Course
Stay ahead with content based on the latest industry trends and practices.