OSQuery for Security Analyst
OSQuery for Security Analyst
- 4.721 students
- Last updated 25/7/2023
Course Description
This self-paced course is designed to equip Security Analysts with practical skills in OSQuery, a powerful open-source tool for endpoint monitoring and security. You’ll begin with OSQuery basics, learning how to set up and configure it, and progress to crafting advanced queries to monitor system events, analyze logs, and detect anomalies.
Through hands-on labs, you’ll simulate real-world security scenarios and build your capability in incident response and threat hunting. Ideal for SOC Analysts and IT security professionals, this course will empower you to utilize OSQuery for comprehensive endpoint visibility and proactive threat detection.
What You Will Learn
- Install and configure Wireshark for network analysis
- Capture and interpret network packets in real time
- Identify common network protocols and anomalies
- Filter and dissect traffic to find security threats
- Analyze TCP, UDP, and ICMP traffic for threats
- Detect signs of network attacks, such as DDoS and spoofing
- Apply Wireshark in incident response scenarios
- Optimize Wireshark for large-scale traffic monitoring
Pre-requisites
- Basic knowledge of networking concepts
- Some experience with Linux or Windows systems
- Familiarity with network protocols
Course Content
- What is Osquery?
- How Osquery works?
- Installing Osquery on Linux
- Installing Osquery on Windows
- SELECT Statement – Fetching Data from Tables
- WHERE Clause – Filtering the Results
- AND / OR – Combining Multiple Conditions
- ORDER BY and LIMIT – Sorting and Trimming Results
- LIKE and IN – Pattern and Value Matching
- COUNT() and GROUP BY – Aggregating and Grouping Data
- JOINs in Osquery – Combining Related Tables
- Querying live data with
osqueryi - Important Tables
- Osquery config file
- Osquery logs
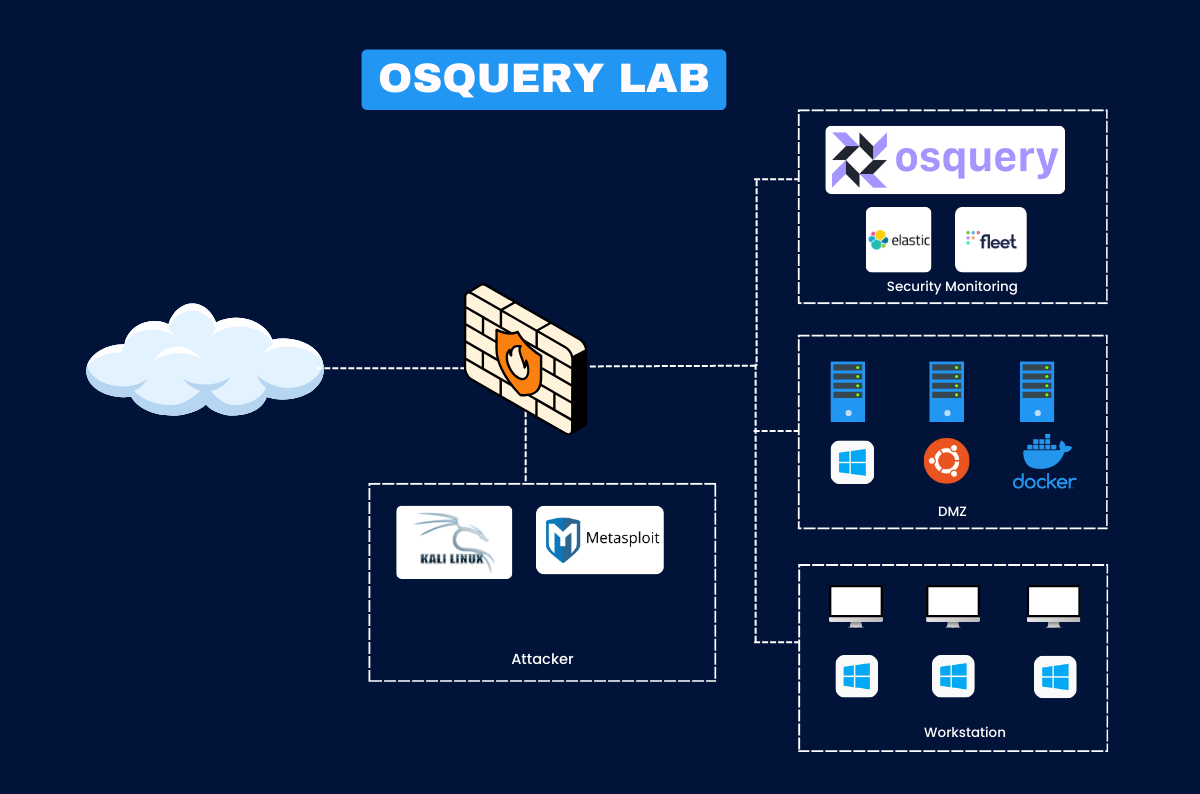
- Setting up ELK
- Setting up Fleet Server
- Setting up Fleet Agent
- Getting started with Osquery
- Detecting New Processes
- Unusual Network Connections
- Scheduled Tasks and Cron Jobs
- USB/External Device Usage
- New User Accounts Created
- Threat Hunting Process
- Hunt#1: PowerShell Abuse via Command Line
- Hypothesis, Data Sources and Indicators
- Attack Simulation
- Hunting for PowerShell Abuse using Osquery
- Hunt#2: Malicious Process from Temp Directory
- Hypothesis, Data Sources and Indicators
- Attack Simulation
- Hunting for Malicious Process
- Hunt#3: Suspicious Scheduled Tasks
- Hypothesis, Data Sources and Indicators
- Attack Simulation
- Hunting for Suspicious Scheduled Tasks
- Hunt#4: Persistence via Startup Items
- Hypothesis, Data Sources and Indicators
- Attack Simulation
- Hunting for Persistence via Startup Items
- Hunt#5: Reverse Shell Execution
- Hypothesis, Data Sources and Indicators
- Attack Simulation
- Hunting for Reverse Shell Execution
Instructor

Senior Security Consultant
- With over a decade of experience in cybersecurity and author of multiple works on security monitoring, Rajneesh is a trusted expert in open-source security tools, cloud security, and SOC automation. He has implemented and optimized ELK deployments for global clients and specializes in turning raw log data into actionable security intelligence. Rajneesh’s instruction style is both practical and thorough, ensuring you gain job-ready ELK skills.
This course includes:
- 8.5+ Hours of Learning Modules
- 10+ Attacks and Detections
- Certificate of Completion
- Lifetime Community Access
- Access on mobile and TV

Testimonial
What alumni say about us






Common Questions
Most Popular Questions
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Ut elit tellus, luctus nec ullamcorper mattis, pulvinar dapibus leo.
Wireshark is an open-source tool that captures and analyzes network traffic in real time. It allows security professionals to examine network packets and identify anomalies, suspicious behavior, and threats at the packet level.
No prior experience with Wireshark is required. The course covers both the basics and advanced concepts, making it suitable for beginners and professionals looking to deepen their expertise.
This course is self-paced, so you can complete it at your own pace. On average, learners take 4-6 weeks to finish, but you have lifetime access to revisit any section.
You'll gain hands-on skills in capturing, filtering, and analyzing network traffic to detect threats. By the end, you'll be able to use Wireshark to recognize various network attacks, identify suspicious patterns, and apply these skills to incident response scenarios.
Yes, we regularly update the content to ensure compatibility with the latest version of Wireshark, covering new features, improvements, and any relevant security techniques.
Yes, upon successful completion, you will receive a certificate from HaxSecurity that you can add to your resume and LinkedIn profile to showcase your Wireshark skills.
You’ll need a computer with a stable internet connection to download Wireshark and capture network traffic. No additional software is required, and detailed setup instructions are provided within the course.
Throughout the course, you can reach out to our support team via email or join our discussion forums to interact with peers. Additionally, Rajneesh hosts periodic live Q&A sessions to address specific questions and provide guidance.
Featured Online Course
Stay ahead with content based on the latest industry trends and practices.