Suricata for Security Analyst
Suricata for Security Analyst
- 4.721 students
- Last updated 25/7/2023
Course Description
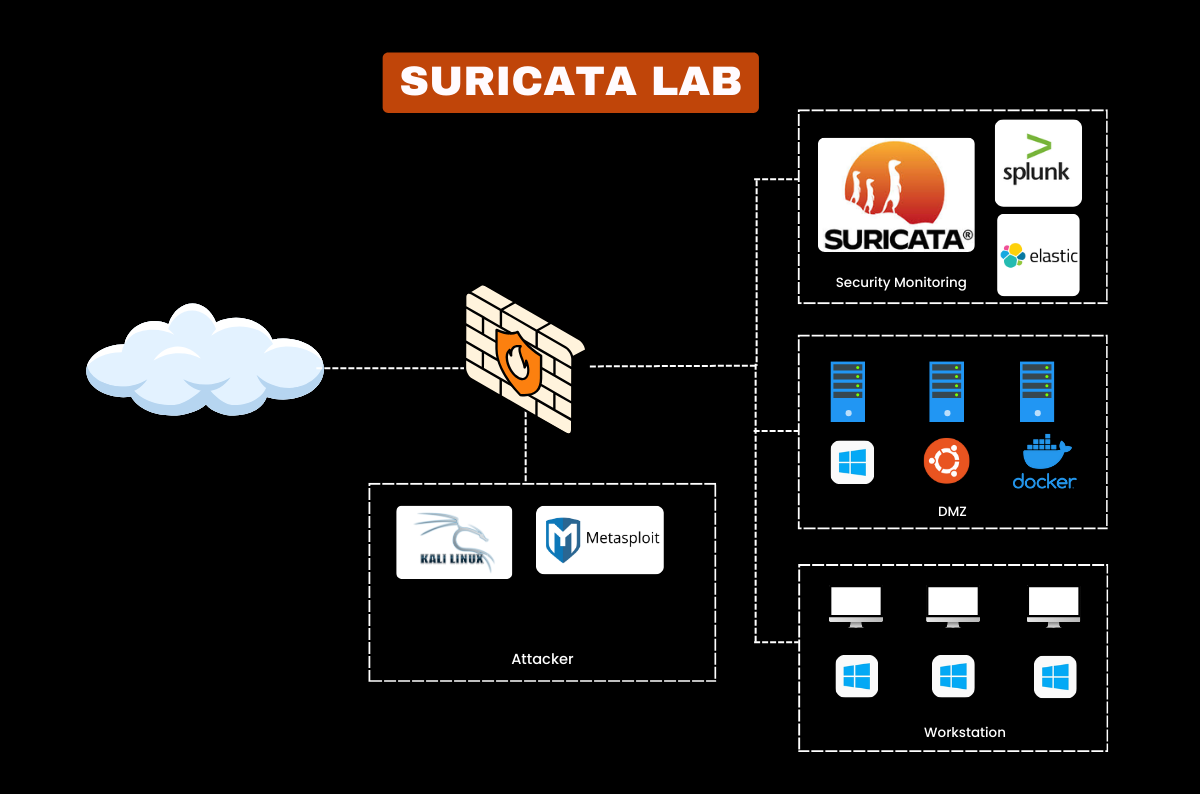
This self-paced course provides you with a deep understanding of Suricata, an open-source network intrusion detection system (NIDS) that is widely used for monitoring and analyzing network traffic for suspicious activities. The course takes you from the essentials of installation and configuration to advanced threat detection techniques using Suricata’s rule sets, protocols, and logs.
Through hands-on labs and real-world examples, you’ll gain practical skills in creating custom alerts, analyzing packets, and detecting anomalies. Ideal for Security Analysts, SOC teams, and anyone eager to specialize in network security, this course will prepare you to handle network-based threats with expertise.
What You Will Learn
- Install and configure Suricata on Linux and Windows
- Understand and apply Suricata rule sets for detection
- Analyze network traffic to detect intrusions
- Configure alerts for suspicious activities in Suricata
- Interpret Suricata logs for threat intelligence
- Integrate Suricata with SIEM tools for SOC operations
- Tune Suricata for optimal performance and accuracy
- Conduct threat hunting using Suricata’s detection capabilities
Pre-requisites
- Basic networking knowledge and security concepts
- Some experience with network protocols and packet analysis
- Familiarity with Linux command line
Course Content
- What is Suricata
- IDS vs IPS
- Suricata Architecture
- Key Features
- Demo: Suricata alerts
- Suricata rules
- Installing Suricata on Ubuntu Machine
- Installing ET rulesets
- Rule Structure and Syntax
- Adding a custom rules
- Installing Splunk on Ubuntu Server
- Setting up Splunk UF on remote Ubuntu Machine
- Installing Suricata on remote Ubuntu machine
- Task#1: Detecting Abnormal Network Traffic
- Setting up Splunk
- Simulating an attack and Analyzing logs on Splunk
- Task#2: Detecting Reverse Shell Detection
- Writing a custom Suricata Rule
- Simulating an attack and Analyzing logs on Splunk
- Task#3: Detecting Unusual File Transfers
- Writing a Suricata Rule over File Transfers over Non-standard Ports
- Simulating an attack and Analyzing logs on Splunk
- Threat Hunting Process
- Hunt#1: DNS Tunneling
- Hypothesis, Data Sources and Indicator
- Hunting for DNS Tunneling Behavior on Splunk
- Creating Splunk Alert
- Hunt#2: Suspicious User-Agent Strings
- Hypothesis, Data Sources and Indicator
- Hunting for Suspicious User-agent on Splunk
- Creating Splunk Alert
- Hunt#3: Unusual TLS Connections
- Hypothesis, Data Sources and Indicator
- Hunting for Unusual TLS Connections on Splunk
- Creating Splunk alert
- Hunt#4: SMB Lateral Movement Attempt
- Hypothesis, Data Sources and Indicator
- Hunting for High Volume of SMB Connections on Splunk
- Creating Splunk Alert
- Hunt#5: High Data Transfer - Exfiltration
- Hypothesis, Data Sources and Indicator
- Hunting for High Data Transfer - Exfiltration on Splunk
- Creating Splunk Alert
- Sending Suricata Alerts to SIEM Tools
- Using Suricata with ELK and Splunk
- Enhancing SOC Capabilities with Suricata Data
Instructor

Senior Security Consultant
- With over a decade of experience in cybersecurity and author of multiple works on security monitoring, Rajneesh is a trusted expert in open-source security tools, cloud security, and SOC automation. He has implemented and optimized ELK deployments for global clients and specializes in turning raw log data into actionable security intelligence. Rajneesh’s instruction style is both practical and thorough, ensuring you gain job-ready ELK skills.
This course includes:
- 7+ hours of hands-on videos
- 16+ Real-World Scenarios
- Certificate of Completion
- Lifetime Community Access
- Access on mobile and TV

Testimonial
What alumni say about us






Common Questions
Most Popular Questions
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Ut elit tellus, luctus nec ullamcorper mattis, pulvinar dapibus leo.
Suricata is an open-source network intrusion detection and prevention system (NIDS/NIPS) that monitors network traffic for suspicious activities. Using rules and protocol analysis, it can detect malicious patterns and alert security teams to potential threats.
No previous experience is needed. This course covers Suricata from the ground up, including installation, configuration, and advanced techniques. Basic networking knowledge is recommended, but we provide foundational lessons to ensure a smooth learning experience.
The course is self-paced, so completion time varies. Most students complete it within 4-6 weeks, but you’ll have lifetime access to revisit modules as needed.
By the end of the course, you’ll be able to set up and configure Suricata, create custom detection rules, analyze network traffic for threats, integrate with SIEM tools, and apply Suricata in real-world threat hunting scenarios. These skills are crucial for network security and SOC roles.
Yes, we update the course regularly to reflect the latest Suricata features and capabilities. The course content is aligned with the most current version, so you’ll learn the latest techniques and best practices.
Yes, you’ll receive a certificate from HaxSecurity upon completion, which you can display on LinkedIn and add to your resume to showcase your Suricata skills.
You’ll need a computer with Suricata installed, ideally on a virtual or physical Linux environment. Detailed installation instructions and setup support are included in the course.
Our support team is available to help with technical questions, and we offer a discussion forum for learners to interact with each other. Additionally, Rajneesh hosts regular live Q&A sessions where you can ask specific questions and gain further insights into the material.
Featured Online Course
Stay ahead with content based on the latest industry trends and practices.